Crack and trace window now supports looking the referencedAddress, referencedBytes and Instruction
In 2017, the Enjoyment Application Affiliation (ESA) sent a copyright infringement discover inquiring Eric Heijnen to cease and desist. The recognize claimed Cheat Engine permitted evading anti-cheat technologies, accessing in-game DLC goods/microtransaction merchandise that could only be acquired with actual revenue. Eric Heijnen responded by shutting down the cheat tables segment to the public, asking them to be hosted off-internet site and coming to an agreement with ESA.
We produced this checklist with google translate, so make sure you elevate a difficulty if you utilize a research expression that doesn't consist of any of such words and phrases or if any on the stated text are incorrect.
Warning: Proceed at your own risk as some games or platforms (like Steam) may well ban your account for making an attempt unethical procedures to manipulate the game modules and working with Cheat Engine. The procedures reviewed right here, are for educational functions only.
Added an automated framework compare for 2 teams of addresses to locate ways to differentiate in between them
The standard Edition will function for lookup conditions such as any in the under text/phrases. It will need to have the complete term (i.e. "google snaking" or "google snaek" is not going to work, due to the fact they don't consist of the word snake)
As of version six.one, Cheat Engine can create game trainers from the tables. When trainers created in this way are generally really large for their supposed reason, frequently employed for tests uses, some are actually released by trainers teams as "closing" variations,[11] and also some well known websites are completely based on CE trainers[twelve] due to the relieve of trainer creation with CE.
It truly is accustomed to allocate nonpaged memory in kernel manner, manually loading the executable picture, and creating a process thread at Driver Entry. Nevertheless, considering that the driving force Entry parameters usually are not truly valid, the motive force needs to be modified for DBVM.
As being a essential tampering prevention measure, the raw source files are encrypted with the use of AES 256, and so are only momentarily decrypted at operate-time with the aforementioned compilation move.
Hotkeys could be repeated by releasing The crucial element and repressing In case the repeat timer has not concluded nonetheless*
[seventy one] In July of that calendar year, documents of small business slides from shows as early as 2017 had been leaked on line by an unidentified hacker. These files unveiled that the Roblox Company was planning to make many adjustments to the platform throughout the world to adjust to Chinese Scripting Online censorship laws, and that just before canceling operations, they were anxious that Tencent would hack the System and try to make a competitor.[74]
Memoryrecord hotkeys exhibiting up from the options window as carry to entrance. The place clicking OK would then set it to that
This brief weblog post demonstrates how custom policies for API Check may be used to assist in the reversing procedure.
Enhance to Microsoft Edge to take advantage of the most recent options, security updates, and specialized assist.
 Jenna Jameson Then & Now!
Jenna Jameson Then & Now! Michael Jordan Then & Now!
Michael Jordan Then & Now!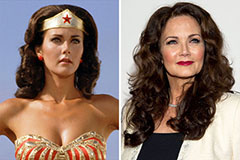 Lynda Carter Then & Now!
Lynda Carter Then & Now! Bo Derek Then & Now!
Bo Derek Then & Now! Nicki Minaj Then & Now!
Nicki Minaj Then & Now!